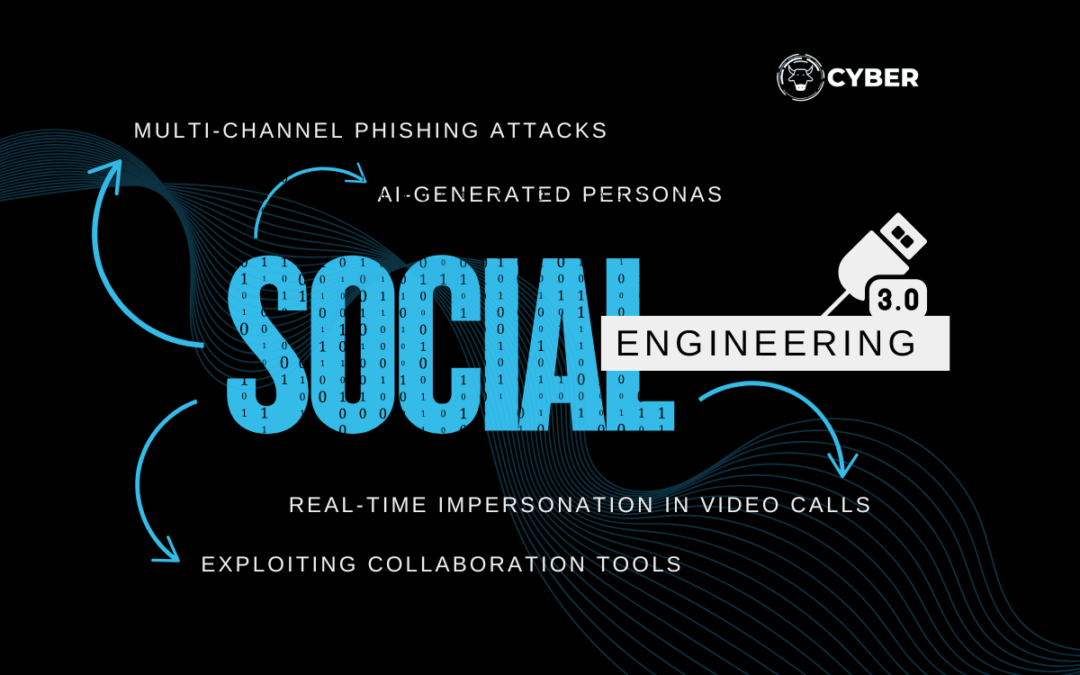
Staying on top of the cybersecurity game means being aware of the latest tactics cybercriminals are using. Social Engineering 3.0 takes traditional scams to new heights, combining advanced technology and psychological manipulation to exploit human behaviour. Understanding these growing threats is crucial to protecting yourself and your organisation.
What Is Social Engineering 3.0?
Social engineering now goes beyond simple scams. Attackers use AI and advanced techniques to create convincing, personalised attacks. These tricks are harder to detect and pose significant risks to individuals and businesses alike.
New Tactics Used by Cybercriminals
- Multi-Channel Phishing Attacks
Attackers use emails, texts, and social media to create multi-step scams. They might follow up phishing emails with calls or messages, tricking victims into giving up sensitive information. - AI-Generated Personas
Cybercriminals use AI to create fake identities, complete with social media profiles, to gain trust and steal sensitive data. - Real-Time Impersonation in Video Calls
Deepfake technology allows cybercriminals to impersonate trusted colleagues in video meetings, facilitating fraud and data breaches. - Exploiting Collaboration Tools
With remote work on the rise, attackers use platforms like Slack and Teams to impersonate colleagues and request sensitive information.
How to Protect Against Social Engineering 3.0
- Implement Zero-Trust Principles: Always verify identities and use multi-factor authentication (MFA).
- Conduct Regular Training: Educate employees on how to recognise social engineering attempts.
- Secure Collaboration Tools: Ensure these platforms are configured with strong security settings.
- Monitor for Unusual Behaviour: Use tools to detect unusual activity in your network.
Social Engineering 3.0 proves that cybersecurity isn’t just about firewalls and encryption—it’s about understanding and addressing human vulnerabilities. By staying informed, training teams, and employing robust security measures, we can stay ahead of even the most sophisticated attacks. Together, we can outsmart cybercriminals and keep our data safe.