by admin | Aug 20, 2025 | Article, Blog
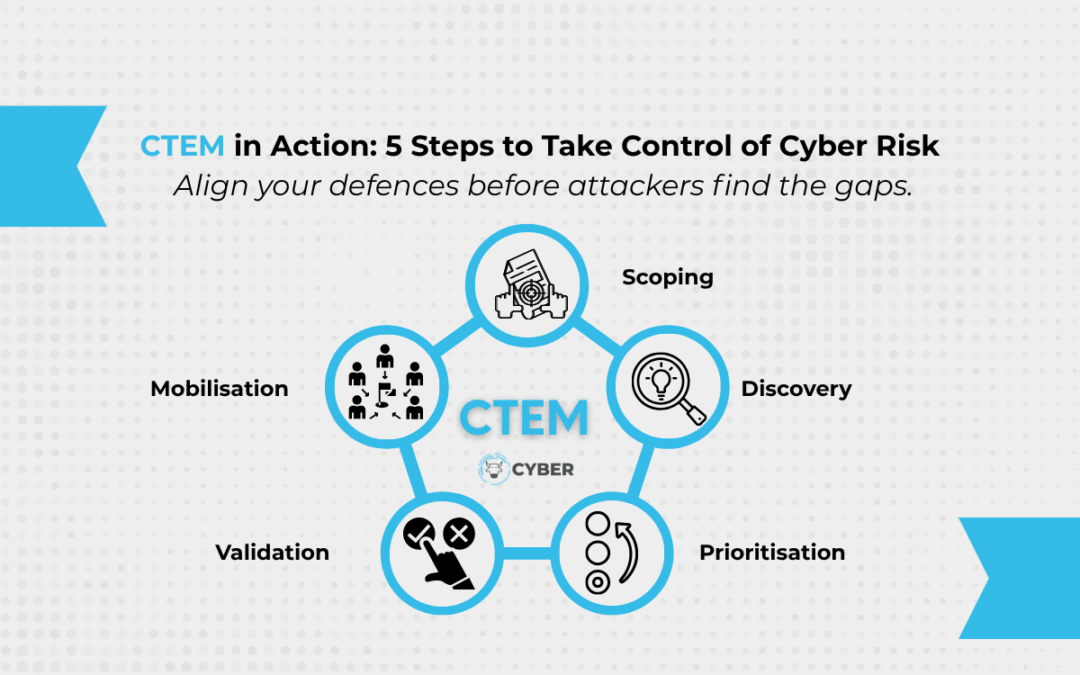
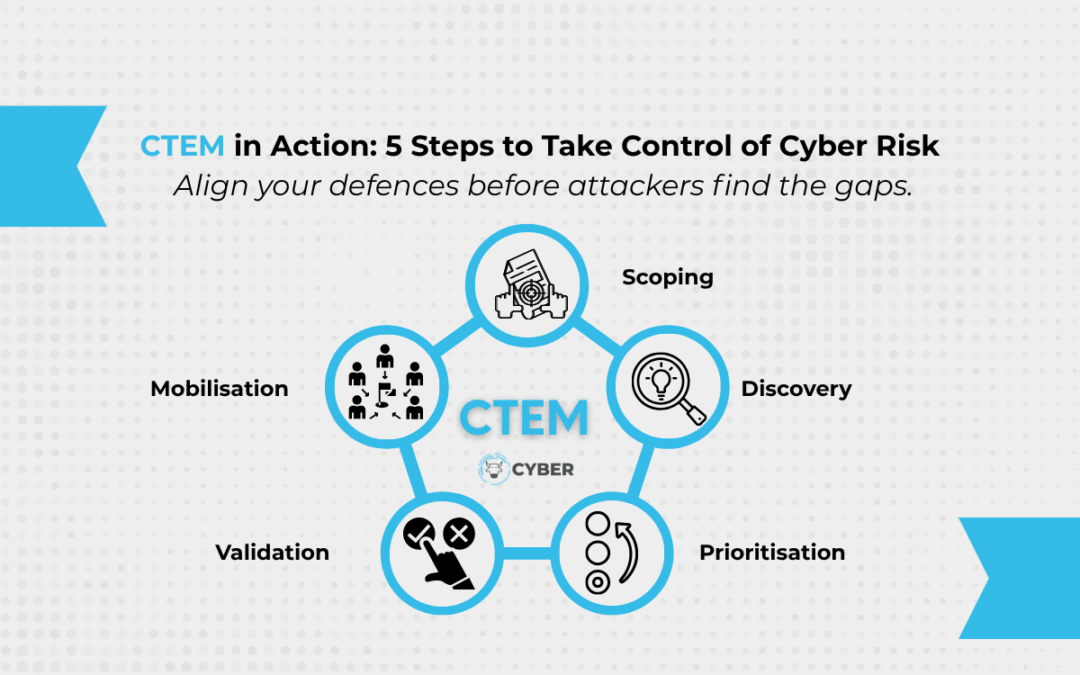
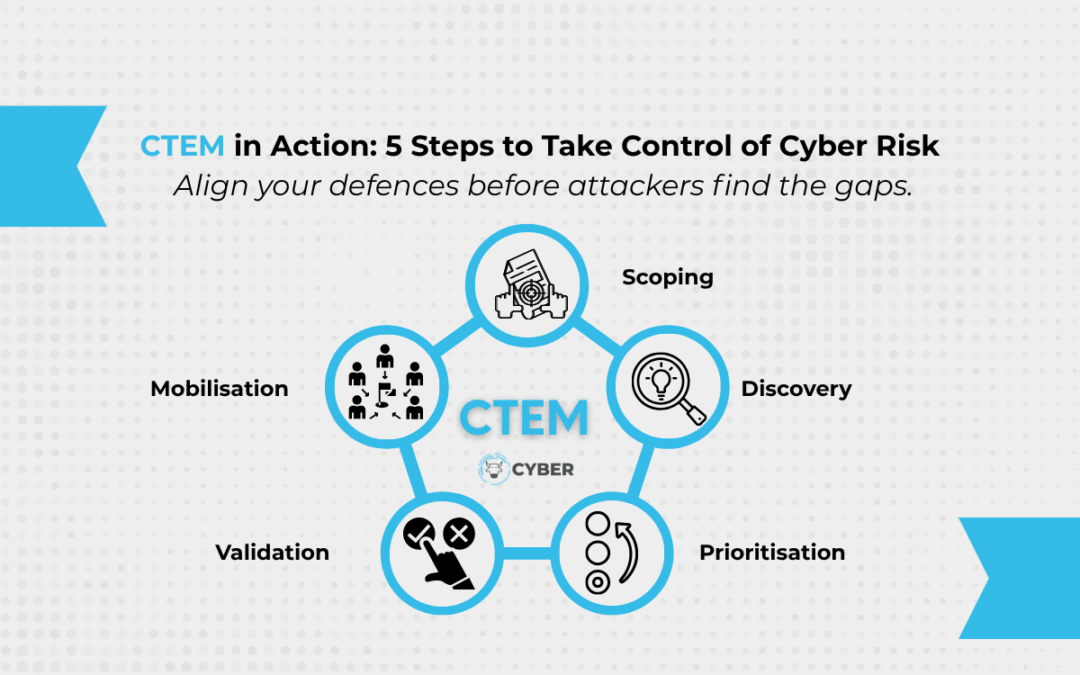
The CTEM Wake-Up Call Most businesses are stuck in a reactive loop when it comes to cybersecurity. If you’re only fixing what’s broken, or chasing the latest threat, you’re not managing risk. You’re managing damage. CTEM flips that. It helps organisations take...
by admin | Aug 13, 2025 | Article, Blog
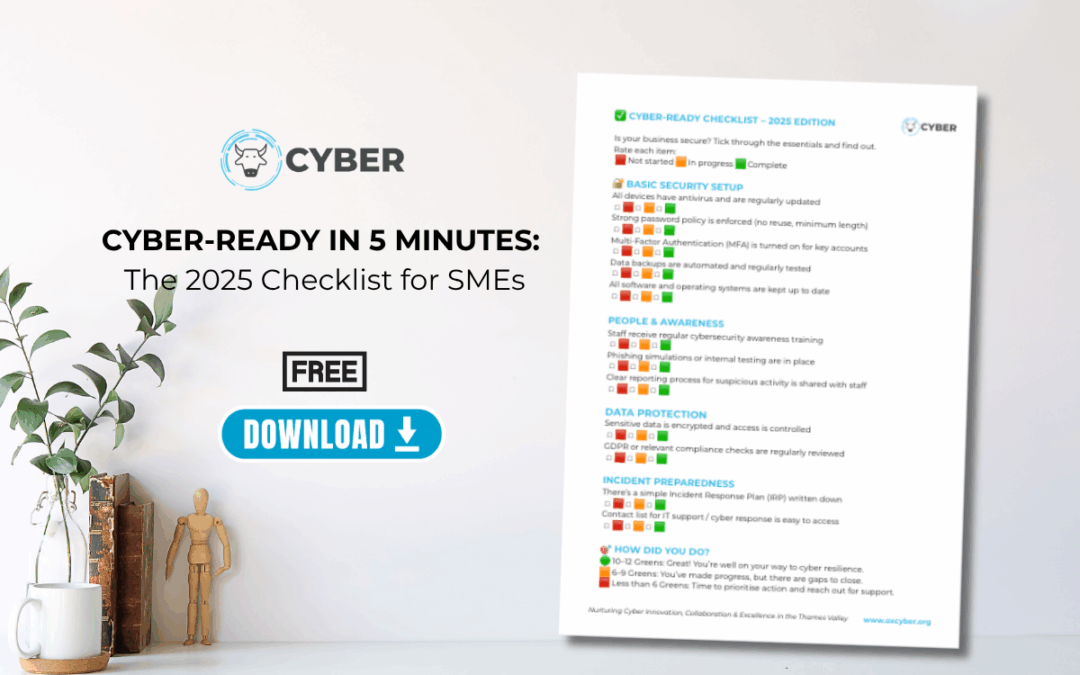
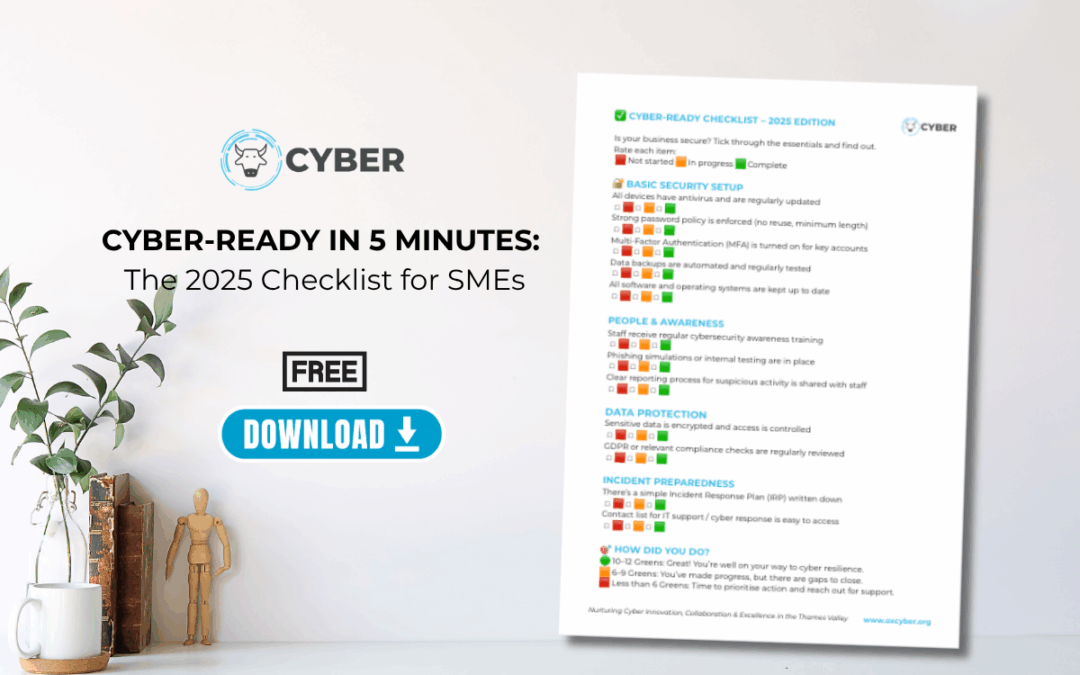
Cybersecurity doesn’t need to be complicated; but it does need to be consistent. One of the most common questions we hear from local businesses, startups, and growing teams across the Thames Valley is simple: “Where do we even start?” So, we’ve made something...
by admin | Aug 6, 2025 | Article, Blog
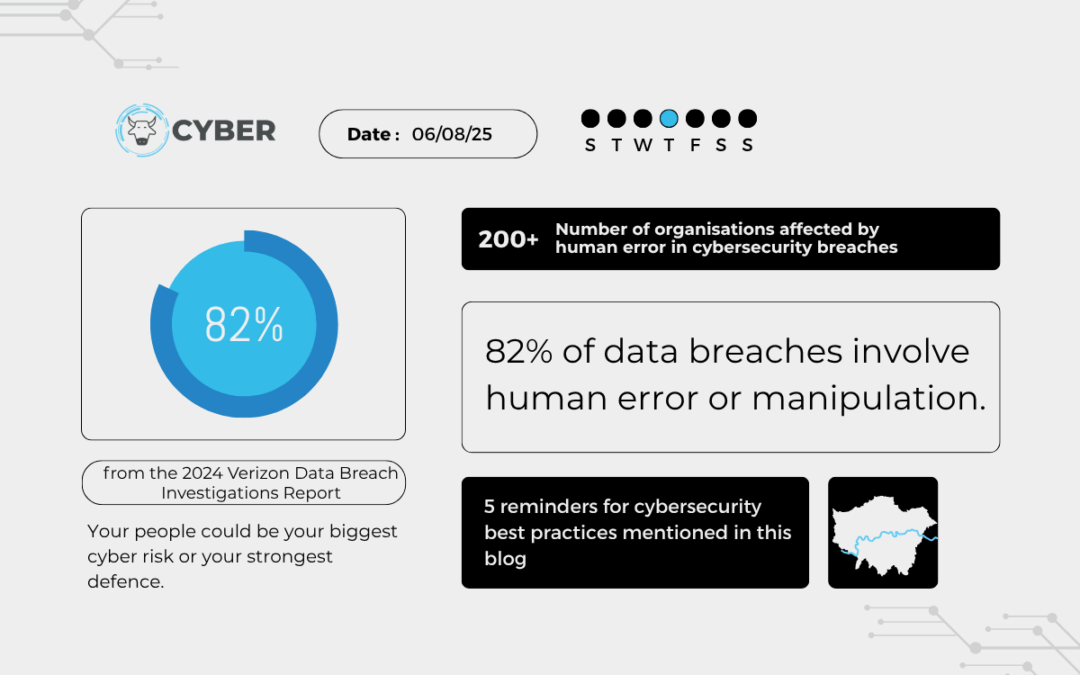
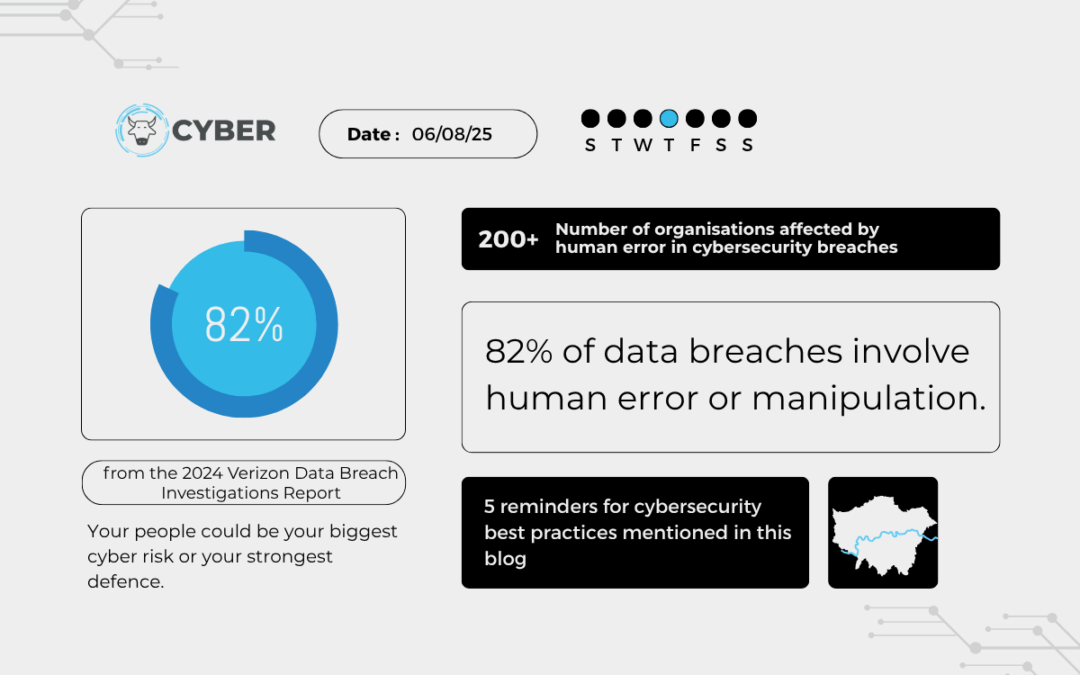
Cybersecurity doesn’t always feel real until it happens to you. But some recent high-profile cases serve as powerful reminders that cyber incidents don’t always start with a sophisticated hacker. Sometimes, it’s just one missed step. One decision. One person. So why...

by admin | Jul 30, 2025 | Article, Blog
It’s easy to picture cybersecurity as something technical. Firewalls, hackers, code. But when you look at the numbers, the real risk often starts with habits. Everyday choices. Little shortcuts we barely notice anymore. That’s what makes the stats so surprising. The...

by admin | Jul 23, 2025 | Article, Blog
We talk a lot about phishing, weak passwords, and social engineering, and rightly so. But lately, we’ve been asking a different kind of question. What happens when attackers don’t just trick us, but actually start influencing how we think? It’s not a sci-fi scenario....

by admin | Jul 16, 2025 | Article, Blog, How To Guide
The modern vehicle is more than just a machine Today’s cars are rolling devices. They collect data. They connect to our phones, our calendars, our smart homes, and our daily routines. They store locations, contact lists, call logs, voice commands, and more. And unless...